DIGITAL MARKETING
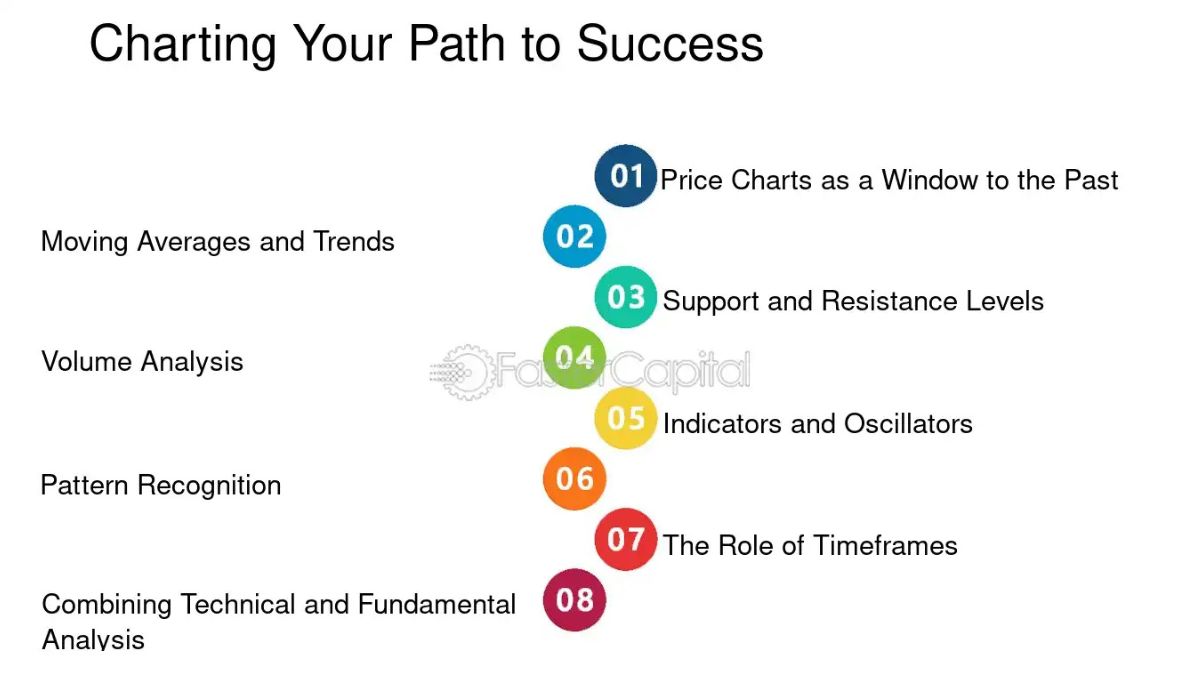
Charting Your Path: From Passion to Influence in the Digital World
In the digital age, opportunities abound for individuals eager to convert their passions into a career in influence. Whether you document travel escapades, showcase culinary creations, or unravel the intricacies of tech gadgets, there’s a niche waiting to be explored. As more enthusiasts contemplate building a career as an influencer, the realm expands with creative, engaging voices that captivate audiences worldwide. Charting a successful course requires strategic planning to resonate with your audience while leaving a stamp of authenticity.
Success in this evolving field mandates a structured approach marked by authenticity and a keen understanding of your audience’s desires. Tapping into methods that have proven effective for countless influencers can guide aspiring individuals through the competitive landscape efficiently and thoughtfully.
Discover Your Niche
In the crowded digital content marketplace, claiming a unique position is crucial for establishing a brand identity. Identifying a niche differentiates you from the masses and ensures you attract and retain the right audience. Consider what genuinely ignites your interest. What unique perspective or expertise do you possess that can serve as your differentiator? Engaging deeply with your interests often leads to the most sincere and effective audience connections.
How to Create Engaging Content
The heart of an influential career lies in the content you create. Exceptional content is captivating and relatable, bridging the gap between influencer and audience. Combining compelling storytelling with stunning visuals adds depth to posts, enriching the viewer’s experience. Continually seek feedback and be open to experimenting with diverse content formats. This flexibility may result in finding innovative methods to captivate your audience and expand your platform. High-quality visuals, heartfelt storytelling, and encouraging interaction are vital elements when creating content.
Tips for Creating Engaging Content:
- Utilize high-quality visuals to enhance the storytelling aspect.
- Incorporate personal stories to create relatable and emotional connections.
- Encourage audience engagement through interactive elements like polls or Q&A sessions.
Strategies to Grow Your Audience
The journey to expanding your follower base goes beyond merely publishing content; it’s about creating lasting relationships that foster trust and engagement. Building a community around common interests allows for more profound connections and interactions. Expanding your presence on various social media platforms creates distinct chances to connect with diverse audience groups.
Strategies to Consider:
- Work with other influencers to access their audience groups and allow them to reach yours.
- Conduct live sessions to engage with your audience instantly, boost visibility, and foster connections.
- Harness the power of authenticity through storytelling to foster a genuine connection with your audience.
Ways to Monetize Your Influence
Once a solid audience foundation is in place, exploring avenues to monetize your influence becomes an exciting next step. Sponsored content, affiliate marketing, and launching personal products or services are viable pathways. Each opportunity aligns differently depending on your brand ethos and audience needs, offering diversification in revenue streams. This adaptability allows you to remain true to your core values while exploring different monetization options.
Maintaining Authenticity for Long-Term Success
In the quest for growth and monetization, maintaining authenticity becomes crucial. Staying true to your values and brand amidst various offers and industry trends preserves the trust and loyalty of your audience. Authenticity ensures you resonate with your audience, allowing for long-term sustainability. A genuine approach protects your brand image and fosters deeper connections, forming a solid foundation for continuous growth and evolution.
Navigating the Challenges
The journey of an influencer is fraught with challenges, from keeping pace with ever-changing algorithms to handling negative feedback or resistance. Navigating these obstacles requires resilience and a readiness to adapt. Welcome the learning process and see obstacles as chances for development. Being prepared and agile in facing setbacks enables you to maintain forward momentum while refining your strategy and approach. Fostering an optimistic attitude and gaining insights from failures encourages a satisfying and enriching journey.
Case Study Examples of Successful Influencers
Observing the journeys of successful influencers can yield rich insights into the mechanisms of influence. Learning from real-world examples provides practical strategies and inventive solutions, empowering you in your path. Each influencer narrative offers valuable lessons that can inspire and guide your unique journey, helping you identify the core strategies that resonate with your goals while fueling your motivation and determination. Embarking on a career as an influencer involves a harmonious blend of strategic planning, authentic engagement, and constant adaptation. Whether you’re a newcomer or further along your path, maintaining a passion-driven mindset makes the journey rewarding. Passion is the catalyst behind your success, fueling genuine connections and creating a resonating impact with your audience, making the digital realm not just a career but a platform for genuine influence.
DIGITAL MARKETING
How to Pick a Reliable Website to Buy Social Media Likes
Engagement is the most important element of social media success, and likes are the most important element in increasing credibility and visibility. Whether you are a business, content creator, or influencer, buying likes can assist in creating social proof and increasing the visibility of your content. But with numerous websites providing social media likes, it is imperative to select a reliable provider to maintain security, authenticity, and long-term gains.
Seek for Authenticity and Real Engagement
The first and the most significant consideration in choosing a site is that it must deliver real likes from genuine users. There are some services that employ bots or fake accounts, which result in artificial engagement without any real worth.
In order to prevent this, go for sites that ensure likes from active and legitimate accounts. You may determine the legitimacy of a service by checking reviews, observing openness in their strategy, and studying sample data from the only site that sells real likes.
Explore Customer Reviews and Reputation
A legitimate site should possess good customer feedback and a superb reputation. Check online reviews, testimonials, and ratings on third-party review sites before buying. Social media groups and discussion forums can also be good predictors of user experiences with different services.
Be cautious of sites with very low customer reviews or no reviews at all. A company with good customer testimonials and a track record of successful customers is in a better position to provide quality engagement and protect your social media account from potential risks.
Look for Privacy Policies and Secure Payment Options
Security is a concern when purchasing social media likes since you may be prompted to provide payment details or account credentials. A good site should offer secure payment options, such as credit card processing that uses encryption. Avoid using sites that ask for your social media password since they will most likely be scams or lead to account hacking.
Also, look at the privacy policy of the website to ensure that your data will not be made accessible to third parties. Good services respect customers’ privacy and clearly state their terms of service.
Assess Delivery Speed, Packages, and Pricing
Though cost is significant, very cheap services are probably signs of low-quality interaction or likes generated by bots. Evaluate several providers and compare their prices relative to the value they bring. Trusted websites will give you clear-cut pricing and options for several package deals so that you can select what suits your requirements best.
Be careful of the speed of delivery too—likes that appear too suddenly tend to look fabricated and get flags on social media sites. Organic, slow-built likes are always better as it keeps your reputation intact and also prevents algorithm punishment.
Check Customer Support and Refund Policies
A good site should have great customer support and a reasonable refund policy. Check for services that offer support via email support, live chat, or a separate help center. If a site has unclear contact information or is slow to respond to questions, it might not be reliable.
Also, check if they have a money-back guarantee in case of low-quality likes or failed services. Platforms that value quality service will have open policies and responsive customer care to guarantee customer satisfaction.
Choosing the only site that sells real likes can help boost engagement, but it’s important to invest in reputable companies that prioritize real likes, gradual delivery, and account security. When done correctly, purchasing likes can be a valuable part of your social media growth strategy, enhancing your online presence and credibility.
DIGITAL MARKETING
How Custom Internal Tools Can Improve Team Collaboration and Productivity

What Are Custom Internal Tools?
Custom internal tools are software solutions designed to meet a company or organization’s unique needs. Unlike off-the-shelf software, these tools are tailored to optimize team workflows and improve efficiency. By addressing a business’s specific challenges, custom tools help streamline processes, reduce time spent on repetitive tasks, and enhance collaboration across departments. Whether for project management, communication, or data processing, custom tools enable teams to focus on their core responsibilities and deliver better results.
With the right custom tools, teams can automate manual tasks and create more seamless workflows. For example, Pythagora offers customizable automation solutions that allow businesses to enhance their development and testing processes. These tailored tools help employees save time, improve productivity, and ensure smoother collaboration. Integrating customized tools into daily activities can help organizations create a more productive and efficient workplace, resulting in improved decision-making and quicker problem-resolution.
Benefits for Team Collaboration
The implementation of custom internal tools significantly enhances team collaboration by breaking down silos within an organization. These tools centralize information and provide a unified platform for team interaction, essential in facilitating smooth communication. Companies that improve their communication strategies see a substantial increase in productivity—up to 25%. Custom tools eliminate the confusion and redundancy that often arise from fragmented communication channels by offering a centralized location for sharing resources, managing tasks, and tracking project progress. This centralized approach streamlines operations and fosters a collaborative atmosphere where team members feel more connected and aligned toward common goals, ultimately driving higher innovation and productivity.
Enhancing Productivity
Tailored internal tools enhance productivity by streamlining regular tasks and allowing employees to concentrate on more important work. These tools’ capacity to optimize processes is unmatched, as they decrease redundancies and cut down the time spent on repetitive tasks. Employing automation through custom software can yield up to a 20% improvement in operational efficiency. This is significant when considering the competitive landscape, as businesses seek to optimize resources and increase output. By providing solutions tailored to business needs, companies can streamline decision-making processes and act quickly on emerging opportunities, thus minimizing bottlenecks. Employees benefit from a more efficient workflow, which maximizes productivity and enhances job satisfaction as they engage in meaningful, impactful work.
Designing Effective Tools
Designing practical internal tools requires a strategic approach based on user engagement and analysis. Using firsthand experiences from end-users, conducting interviews, surveys, and direct observation can help identify pain points, workflow inefficiencies, and feature preferences. Constructive feedback at multiple stages of the development process ensures the tools are user-friendly and aligned with actual work practices.
Semi-simple integration with existing systems is crucial to avoid operational disruptions and ensure high user adoption rates. It is essential to work closely with IT departments to understand technical constraints and test interoperability with various software environments.
Continuous iteration and rigorous testing should be standard practice, incorporating agile methodologies for frequent updates based on user feedback and evolving requirements. Rigorous testing phases, including unit testing, system testing, and user acceptance testing (UAT), should be implemented to identify bugs and ensure reliability.
Adopting analytics and performance metrics post-deployment can guide future enhancements and facilitate a proactive approach to addressing any issues. This dedication to flexibility guarantees that the tools stay pertinent despite technological progress and prepares organizations to react efficiently to changing business landscapes.
Considerations and Challenges
Despite their advantages, custom internal tools have challenges that require careful consideration. The initial investment for developing bespoke solutions can be higher than purchasing ready-made software, and it often necessitates navigating a learning curve for employees. Strong training initiatives ensure a seamless transition and promote widespread acceptance. Additionally, data security is a critical factor; organizations must implement thorough strategies to safeguard sensitive data, ensuring that tools are protected from breaches and unauthorized access. While these challenges are present, effectively tackling them can lead to successful execution and enduring advantages.
DIGITAL MARKETING
From Viral to Valuable: Creating Impactful Social Media Marketing Campaigns

In today’s digital-first world, social media marketing has become a cornerstone of brand growth and customer engagement. While going viral might seem like the ultimate goal, the true measure of success lies in creating campaigns that deliver long-term value. This article explores how businesses can transition from chasing viral moments to building impactful, value-driven social media marketing campaigns that resonate with audiences and drive meaningful results.
The Allure of Viral Social Media Marketing
The idea of going viral is undeniably appealing. A single post, video, or hashtag can catapult a brand into the spotlight, generating millions of views, shares, and likes overnight. Viral campaigns often create a sense of instant success, but they come with a caveat: virality is fleeting.
While viral moments can boost visibility, they don’t always translate into sustained engagement or conversions. For example, a funny meme might get shared widely, but if it doesn’t align with your brand’s core message or target audience, it may fail to drive meaningful results. This is where the shift from viral to valuable becomes crucial.
What Makes a Social Media Marketing Campaign Valuable?
A valuable social media marketing campaign goes beyond likes and shares. It focuses on creating meaningful connections with your audience, driving actionable outcomes, and aligning with your brand’s long-term goals. Here are the key elements of a valuable campaign:
- Audience-Centric Content
Understanding your audience is the foundation of any successful social media marketing strategy. Valuable campaigns are tailored to the needs, preferences, and pain points of your target demographic. Use analytics tools to gather insights about your audience’s behavior, interests, and engagement patterns. - Clear Objectives
Every campaign should have a defined purpose. Whether it’s increasing brand awareness, driving website traffic, or boosting sales, your goals should guide your content creation and distribution strategy. - Authenticity and Storytelling
Audiences crave authenticity. Share stories that reflect your brand’s values, mission, and personality. Authentic storytelling fosters trust and emotional connections, making your campaigns more memorable and impactful. - Consistency
Consistency in tone, style, and posting frequency helps build brand recognition and loyalty. A valuable campaign isn’t a one-off effort; it’s part of a cohesive social media marketing strategy. - Measurable Results
A valuable campaign is one that delivers measurable outcomes. Use metrics like engagement rates, click-through rates, and conversion rates to evaluate the success of your efforts and make data-driven improvements.
Steps to Create Impactful Social Media Marketing Campaigns
1. Define Your Goals and KPIs
Before launching a campaign, clarify what you want to achieve. Are you looking to increase followers, generate leads, or promote a new product? Set specific, measurable goals and identify key performance indicators (KPIs) to track your progress.
2. Know Your Audience
Conduct thorough research to understand your audience’s demographics, interests, and online behavior. Use this information to create content that resonates with them. Tools like Facebook Insights, Instagram Analytics, and Google Analytics can provide valuable data.
3. Craft Compelling Content
Content is the heart of any social media marketing campaign. Focus on creating high-quality, visually appealing, and engaging content that aligns with your brand’s voice. Experiment with different formats, such as videos, infographics, polls, and user-generated content, to keep your audience engaged.
4. Leverage Storytelling
Stories have the power to evoke emotions and drive action. Share behind-the-scenes glimpses, customer success stories, or narratives that highlight your brand’s mission. For example, Dove’s “Real Beauty” campaign used storytelling to challenge beauty stereotypes, creating a lasting impact.
5. Engage with Your Audience
Social media is a two-way street. Respond to comments, messages, and mentions to foster a sense of community. Encourage user-generated content by running contests or asking followers to share their experiences with your brand.
6. Collaborate with Influencers
Influencer partnerships can amplify your reach and credibility. Choose influencers whose values align with your brand and whose followers match your target audience. Micro-influencers, in particular, often have highly engaged audiences and can deliver strong results.
7. Optimize for Each Platform
Different social media platforms have unique features and audience expectations. Tailor your content to suit each platform. For example, Instagram favors visually-driven content, while LinkedIn is ideal for professional and thought-leadership posts.
8. Monitor and Adjust
Track your campaign’s performance using analytics tools. Identify what’s working and what’s not, and make adjustments accordingly. A/B testing can help you refine your approach and maximize your results.
Examples of Valuable Social Media Marketing Campaigns
- Nike’s “Just Do It” Campaign
Nike’s campaign is a prime example of value-driven social media marketing. By focusing on empowerment and inclusivity, Nike has created a lasting connection with its audience, transcending the pursuit of virality. - Starbucks’ #RedCupContest
Starbucks’ annual holiday campaign encourages customers to share photos of their red cups for a chance to win prizes. This user-generated content strategy not only boosts engagement but also creates a sense of community around the brand. - Airbnb’s #WeAccept Campaign
Airbnb’s campaign promoting diversity and acceptance resonated deeply with its audience. By aligning with a social cause, Airbnb demonstrated its values and strengthened its brand identity.
The Long-Term Impact of Valuable Campaigns
While viral moments can provide a temporary boost, valuable social media marketing campaigns deliver long-term benefits. They build brand loyalty, foster customer relationships, and drive sustainable growth. By focusing on creating meaningful content and engaging with your audience authentically, you can turn fleeting attention into lasting impact.
Conclusion
In the ever-evolving landscape of social media marketing, the shift from viral to valuable is essential for long-term success. By prioritizing audience-centric content, clear objectives, and measurable results, businesses can create campaigns that not only capture attention but also drive meaningful outcomes. Remember, the true power of social media marketing lies in its ability to build connections, inspire action, and deliver value—one post at a time.
-

 BLOG2 years ago
BLOG2 years agoATFBooru: A Hub for Animated Art and Community
-

 CONSTRUCTION1 year ago
CONSTRUCTION1 year agoBuilding a Home Gym in Your Basement (7 Key Renovation Tips)
-

 BLOG2 years ago
BLOG2 years agoFictionmania: A Deep Dive into the World of Transformative Stories
-

 LIFESTYLE1 year ago
LIFESTYLE1 year agoVersatile Living: Stylish Indoor Outdoor Rugs with Eco-Friendly Appeal
-

 LIFESTYLE1 year ago
LIFESTYLE1 year agoAchieve Elegance with Chic Blue Formal Dresses and Redken Professional Hair Care for All Hair Types
-

 GAMES1 year ago
GAMES1 year agoSnow Rider 3D: Unblocked Tips and Tricks for Gamers
-

 BLOG1 year ago
BLOG1 year agoGIFHQ: A Comprehensive Guide
-

 BLOG1 year ago
BLOG1 year agoVincent herbert new wife: A Detailed Overview
